Placements Companies
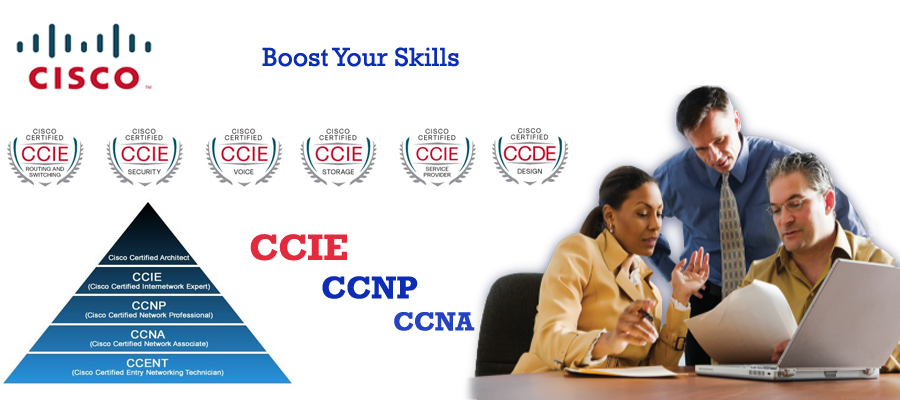
Boost Your Career and IT Skills | Get 30% Hike on Salary
Join Job Oriented CCNP Program
Live Project Training
This shows that Rexton IT Solutions recognizes your skill and support you throughout the training program. The course basically focuses on wireless networking principles and theory. With this CCNP Wireless program, one can identify the technical acumen and expertise of wireless programming. You will be able to access and convert the network business needs to the technical specifications.
The team in Rexton IT Solution is leveraged with the experts of their own trait and knows the basics to teach the students. The learning environment is favourable to the students and offers individual, corporate, live project, professional and industrial training. We understand the needs of the students and know what is best for their future or career. We collaborate with more than 500 registered companies and our trained students are successfully working in numerous MNCs and drawing handsome salary figure.
The Cisco Certified Network Professional (CCNP) Wireless is regarded as a middle-level certification course done by thousands of people who want to make their career in wireless networking. Our course is designed to recognize your expertise as a wireless professional by learning the theory and principles related to it. At Rexton IT Solutions, the professional will teach you regarding the implementation, operation, and design of the Cisco wireless networks along with mobility infrastructures. On completion, you are ready for finding and translating the network business requirements to the technical specifications.
We offer the access of labs to 24x 7 so that you can practice the verbal knowledge and understand the networking things better. With this course, you can become capable of figuring out and fixing all types of network related issues. Not only this, you can design, implement and secure the Cisco Wireless Networks to promote the optimal working.
CCNA | CCNP | CCIE | LINUX | MCSA | MCSE | OFFICE 365 | VMWARE | AZURE | AWS-CLOUD | SQL | ORACLE | JAVA | PYTHON | DEVOPS | KUBERNETES | CHECKPOINT | PALOALTO | FORTENET | F5-LOAD BALANCER | ROBOTICS | RPA | BLUEPRISM | MACHINE LEARNING | ITIL
| Exam | Recommended Training |
|---|---|
| 300-360 WIDESIGN | EXAM-1 Designing Cisco Wireless Enterprise Networks [300-360 WIDESIGN] |
| 300-365 WIDEPLOY | EXAM-2 Deploying Cisco Wireless Enterprise Networks [300-365 WIDEPLOY] |
| 300-370 WITSHOOT | EXAM-3 Troubleshooting Cisco Wireless Enterprise Networks [300-370 WITSHOOT] |
| 300-375 WISECURE | EXAM-4 Securing Cisco Wireless Enterprise Networks [300-375 WISECURE].pdf |
- 1.0 Obtaining Customer Requirements as Related to the WLAN Installation
- 2.0 Determine Facility Type and Constraints Related to WLAN Deployments
- 3.0 WLAN Predictive Design
- 4.0 Pre-Deployment Site Survey
- 5.0 Post-Deployment Site Survey
- 6.0 Design the Infrastructure of the Wireless Network
- 7.0 Describe and Design Wireless Architecture for Real-time Applications
- 1.0 Implement QoS for Wireless Applications
- 2.0 Implement Multicast over Wireless
- 3.0 Implement High Density
- 4.0 Design and Deploy WLAN Infrastructure for Mobility
- 5.0 Implement Cisco MSE Architecture
- 6.0 Design and Implement FlexConnect Architecture
- 7.0 Implement Controller and AP High Availability
- 8.0 Wireless Bridging (MESH)
- 1.0 Troubleshooting Methodology
- 2.0 Troubleshoot AP Joining Issues
- 3.0 Troubleshoot Client Connectivity Issues
- 4.0 Identify and Locate RF Interferences
- 5.0 Troubleshoot Client Performance Issues
- 6.0 Identify Common Wired Infrastructure Issues Based on the Output From Common Troubleshooting Tools
- 7.0 Troubleshoot WLC and AP High Availability Issues
- 1.0 Integrate Client Device Security
- 2.0 Implement Secure Distribution System Connectivity Services on the Wireless Infrastructure
- 3.0 Implement Secure Client Connectivity Services on the Wireless Infrastructure
- 4.0 Implement Secure Management Access on the WLAN Infrastructure
- 5.0 Monitoring Security on the WLAN Infrastructure
- 300-360 WIDESIGN
- Number of questions: 55-65 questions
- Exam duration: 90 Minutes
- Languages: English
- 300-365 WIDEPLOY
- Number of questions: 55-65 questions
- Exam duration: 90 Minutes
- Languages: English
- 300-375 WISECURE
- Number of questions: 55-65 questions
- Exam duration: 90 Minutes
- Languages: English
- 300-370 WITSHOOT
- Number of questions: 55-65 questions
- Exam duration: 90 Minutes
- Languages: English
Exam Track
You'll sit the following exams at the REXTON institute Centre during the course, covered by your Certification Guarantee:



_4.jpg)
_3.jpg)
(1).jpg)
.jpg)
(1).jpg)
(1).jpg)
(1).jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)