_2.jpg)
Placements Companies
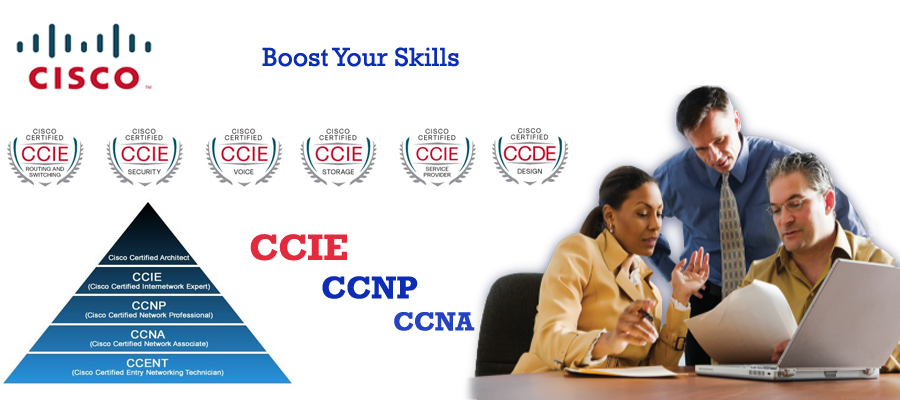
CCNP Live Project Training
Rexton IT Solutions is a recognized training center in Noida who is keenly offering the CCNP security course to those who wants to make their future in the security industry.
Cisco Certified Network Professional (CCNP) Security is a certification program done by many people to get the job of Cisco Network Security Engineer who is accountable for maintaining the security in switches, routers, aznetworking devices, and appliances. Along with this, they can also choose, deploy, support and troubleshoot the problems related to the VPNs, Firewalls and IDS/IPS for different networking environments. If you also want to have excellent hands-on experience, then Rexton IT Solutions is the best place to do that. In our institute expert's trainers are proficient enough to make you learn the fundamentals of this course. Our infrastructure is well built and friendly for attaining professional, corporate, industrial and live project training. The CCNP Security labs are also open for 24x7 so that our students can take the hands-on experience to understand the course well.
The offered training program by Rexton IT Solutions is open to all and available at the competitive prices. We are honored to place more than thousands of students in different multinational companies. After completion of your certification process, based on your skills, we assure you the 100% job satisfaction.
Considered as the intermediate level certification program, Cisco Certified Network Professional (CCNP) Security training is meant for network security engineer and administrators. Basically, they work with both local and wide area network. On completion, the candidates are capable of the implement and configure the router security, networking devices, appliances, and switches. Not only this, they are also responsible for choosing, supporting, deploying and troubleshooting the VPNs, IDS/IPS solutions for numerous networking environments. Their expertise also allows them to work with the specialists to provide the advanced security.
The course allows you to figure out and fix the problem. Our students doing the excellent jobs in the sectors like telecommunications, financial services, Information Technology services, Network security, IT consulting and communication services.
Rexton IT Solutions CCNP Security institute provides online training and classroom training. You can learn CCNP Security online and CCNP Security Course Offline. CCNP Security institute in Noida give you a better career and growth. Rexton CCNP Security training institute provides good lab setup for CCNP Security course. There are numerous CCNP Security certification and online training courses available to help you prepare for the CCNP Security exam. CCNP Security online course is created to help you pass the CCNP Security exam. While attaining a CCNP Security certification confirms that you have the necessary training, expertise, knowledge, and devotion. CCNP Security course online is very easy. We are providing CCNP Security course online if you wants a good career in cisco Networking. In CCNP Security Training Institute in Noida, you will work in the live programs which are the same as the real industry. Our CCNP Security class online is Instructor Led Training and Rexton is a best CCNP Security institute Noida. CCNP Security training institute provides 100% job if you lean CCNP Security course.

| Exam | Recommended Training |
|---|---|
| 350-701 SCOR | Implementing and Operating Cisco Security Core Technologies (SCOR) v1.0 |
| 300-710 SNCF | Securing Networks with Cisco Firepower Next Generation Firewall (SSNGFW) v1.0 |
| 300-715 SISE | Implementing and Configuring Cisco Identity Services Engine (SISE) v3.0 |
The CCNP Security certification program prepares you for today’s professional-level job roles in security technologies. One of the industry’s most respected certifications, CCNP validates the core knowledge you need while providing the flexibility to choose a focus area.
To earn CCNP Security, you pass two exams: a core exam and a concentration exam of your choice.
The core exam, Implementing and Operating Cisco Security Core Technologies v1.0 (350-701 SCOR), focuses on your knowledge of security infrastructure including network security, cloud security, content security, endpoint protection and detection, secure network access, visibility, and enforcements. You can prepare for this exam by taking the training course, Implementing and Operating Cisco Security Core Technologies (SCOR).
The core exam is also the qualifying exam for CCIE Security certification. Passing this exam helps toward earning both of these certifications Concentration exams focus on emerging and industry-specific topics such as Cisco Firepower, identity services, email security, web security, VPNs, and automation. You can prepare for concentration exams by taking corresponding Cisco training courses.
Choose your CCNP Security concentration exam from these options:-
• Securing Networks with Cisco Firepower (300-710 SNCF)
• Implementing and Configuring Cisco Identity Services
Engine (300-715 SISE)
• Securing Email with Cisco Email Security Appliance
(300-720 SESA)
• Securing the Web with Cisco Web Security Appliance
(300-725 SWSA)
• Implementing Secure Solutions with Virtual Private Networks
(300-730 SVPN)
• Automating and Programming Cisco Security Solutions
(300-735 SAUTO)



_4.jpg)
_3.jpg)
(1).jpg)
.jpg)
(1).jpg)
(1).jpg)
(1).jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)